Overcome three core digital transformation challenges to achieve resilient security
Solutions

Resilient Identity
Authentication & Access Management
We create robust access control to your business applications (either cloud or on-premise) or resources through strong authentication protocols and identity proofing. Our unique strategy protects the digital identity of your employees, business partners and customers.
Identity Lifecycle Management
Identity lifecycle management is crucial for resilient cybersecurity. We implement reliable processes to onboard, offboard or change users to protect your data and assets and ensure you are compliant with business regulations.
Identity Governance & Administration
Automate, manage and review access rights and business roles within your application landscape to help your organisation effectively address today’s complex business challenges.
Privileged Access Management
Secure your business-critical assets with our Privileged Account Management solution, which allows you to secure your infrastructure and applications, run your business efficiently and successfully maintain the confidentiality of your sensitive data and critical infrastructure.

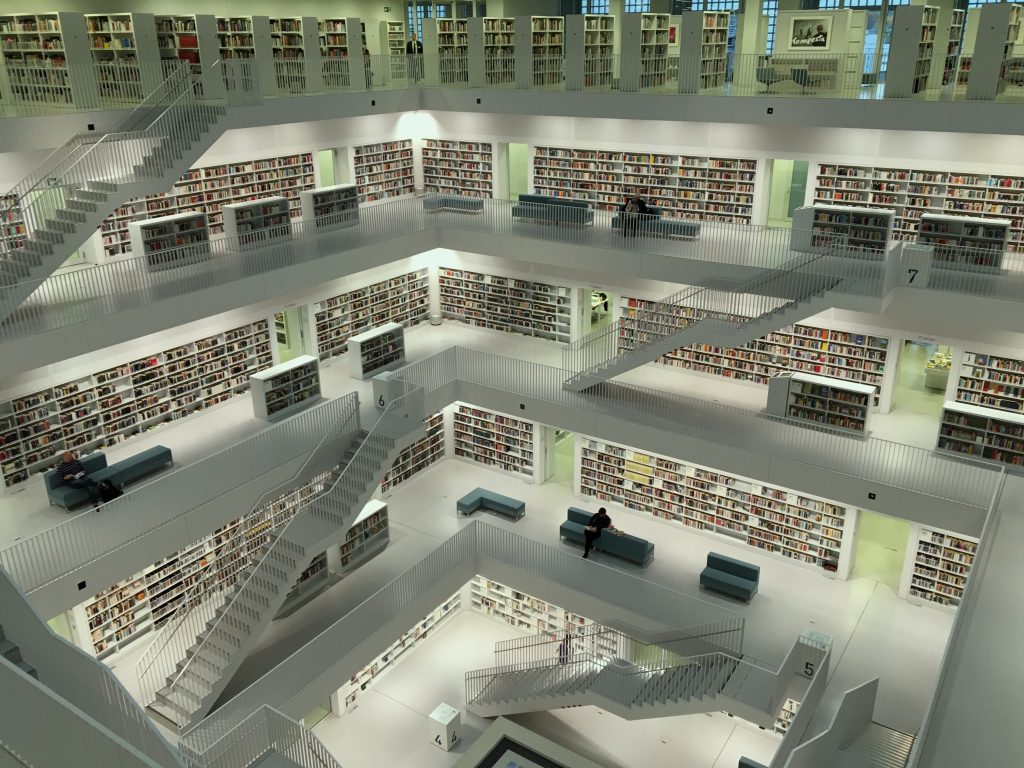
Secure digital identities are your first line of defence
Resilient Data
Data Governance
Data is your organisation’s most prized possession. Governance is essential to determine who can access what kinds of data, what is gathered, what and where it is stored, how it’s processed and even when/where it is disposed of. Meanwhile, regulation and compliance is a driving factor for many organisations to ramp up their cybersecurity and ensure adherence to avoid costly and reputation-damaging breaches.
Data Classification
Knowing and understanding your data types is essential for determining what level of security each needs. Whether its personal information, intellectual property, business-critical data or any other sensitive information, manual or automated classification is the starting point from which you can enforce robust security measures.
Data Loss Prevention
After governance and classification are taken care of, data loss prevention should be a priority. A Data Loss Prevention strategy that is designed based on the classifications of your data will help prevent data loss caused by security breaches like malicious threats, accidental sharing or theft.
Data protection measures
Apply flexible protection based on data types and policies in your DLP strategy, such as encryption, access restrictions or visual markings. Let our team guide you on the best data protection measures for your organisation.
Resilient data ensures business continuity despite unexpected disruption
Resilient Workplace
Endpoint Governance
Endpoint governance ensures there are policies and processes in place to control your devices and protect your networks from unauthorised access. Out teams can help you determine robust endpoint governance based on your specific security needs.
Endpoint security baseline
Your organisation’s security edge is constantly evolving. Remote workers and their endpoints need to be as secure as possible, without restricting workforce mobility, agility and productivity. We’ll define a secure endpoint baseline and ensure you have the right strategy in place to meet all compliance and legislative requirements, enabling you to work, communicate and collaborate with confidence.
Endpoint Detection and Response
Endpoint detection and response will provide monitoring and data collection to detect threats and anomalies. Our security analysts can effectively prioritise alerts, achieve full visibility of the breach and react quickly to remediate threats.
Vulnerability Management
Identify, assess and remediate endpoint weaknesses to reduce risks to your organisation with our threat and vulnerability management solution.

Endpoint management ensures a unified approach to security, without compromising workforce mobility, agility and productivity
Resilient Cloud
Cloud infrastructure entitlement management
Manage identities and access privileges in a multi-cloud environment and guarantee that the least privilege principle is always applied and part of your cloud strategy.
Cloud security posture management
Detect misconfigurations and ensure that you remain compliant with the latest regulations with our cloud security posture management approach.
Extended detection and response
Comprehensive monitoring and early threat/anomaly identification with our extended detection and response security approach. Gain full visibility of events happening in your multi-cloud environment and react quickly to keep your assets secure.
Vulnerability management
Identify, assess and remediate weaknesses of your workloads deployed in the cloud and start to reduce risks to your organisation with our threat and vulnerability management solution.
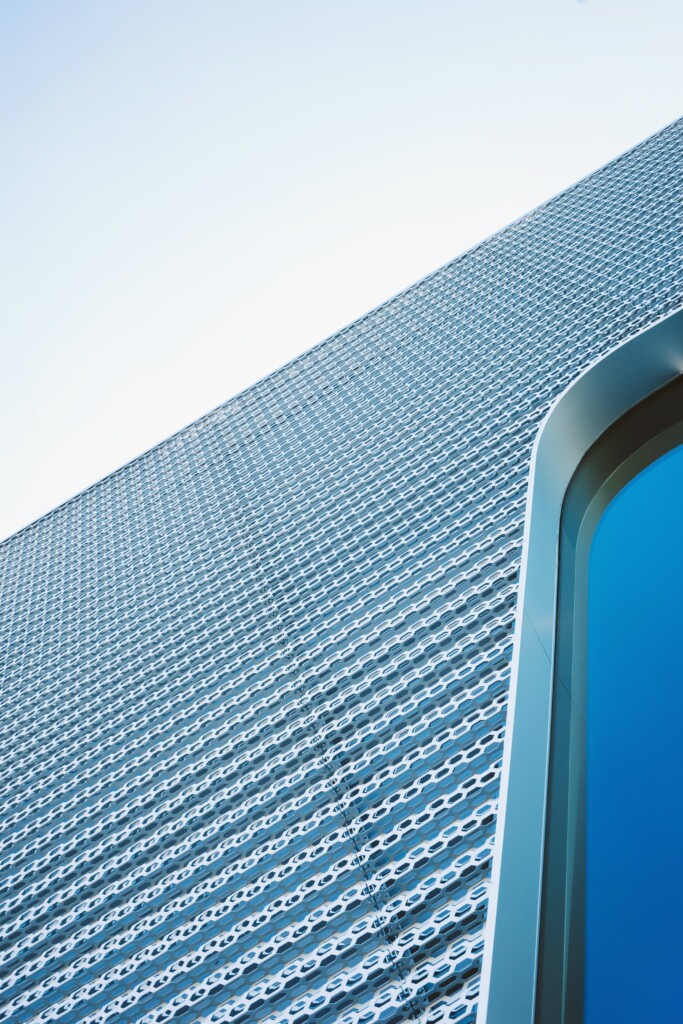
Manage your security posture in a multi-cloud approach
